How the 11th Circuit's 'Wooden Application of the Third-Party Doctrine' Threatens Privacy
The court's cellphone decision implies that remotely stored information has no Fourth Amendment protection.
As Scott Shackford noted earlier today, the U.S. Court of Appeals for the 11th Circuit yesterday overturned a 2014 panel decision requiring a probable-cause warrant to obtain cellphone location records. Last year, in a case involving an armed robber named Quartavius Davis who was linked to the scenes of various crimes by cellphone data, a three-judge 11th Circuit panel concluded that people have a reasonable expectation of privacy in such information, which can reveal where you are throughout the day, every day. The full court disagreed, saying that claim is foreclosed by the Supreme Court's "third-party doctrine," which holds that "a person has no legitimate expectation of privacy in information he voluntarily turns over to third parties." The Court also has said "the Fourth Amendment does not prohibit the obtaining of information revealed to a third party and conveyed by him to Government authorities, even if the information is revealed on the assumption that it will be used only for a limited purpose and the confidence placed in the third party will not be betrayed."
Given the sweeping language of those precedents, you can see why the 11th Circuit ruled the way it did, joining two other circuits (the 5th and 6th) that have reached the same conclusion. The three judges who signed last year's decision and the two dissenters from yesterday's ruling tried to avoid that result by arguing that cellphone users do not voluntarily disclose their locations when they make and receive calls and may not even realize their service providers collect and store that information. Nonsense, says the full court:
Cell users know that they must transmit signals to cell towers within range, that the cell tower functions as the equipment that connects the calls, that users when making or receiving calls are necessarily conveying or exposing to their service provider their general location within that cell tower's range, and that cell phone companies make records of cell-tower usage. Users are aware that cell phones do not work when they are outside the range of the provider company's cell tower network. Indeed, the fact that Davis registered his cell phone under a fictitious alias tends to demonstrate his understanding that such cell tower location information is collected by MetroPCS and may be used to incriminate him.
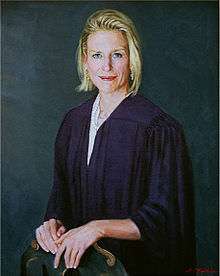
Then again, maybe not. As Judge Beverly Martin (who also joined last year's decision) notes in her dissent, statements by the prosecution in this case suggest that cellphone users do not necessarily realize they are carrying tracking devices. "What this defendant could not have known was that…his cell phone was tracking his every moment," a prosecutor said during Davis' trial. The government also observed that Davis and his accomplices "had no idea that by bringing their cell phones with them to these robberies they were allowing MetroPCS and now [the jury] to follow their movements."
Whether or not Davis recognized the privacy implications of carrying a cellphone, ignorance of that subject is a pretty thin reed on which to hang a warrant requirement, as I noted in a column last year. Once you understand how cellphones work, do you lose any Fourth Amendment interest in the information about your whereabouts revealed by the spy in your pocket? Under the 11th Circuit's reasoning, you do. Martin notes that the data obtained without a warrant in this case covered 67 days, during which "Mr. Davis made or received 5,803 phone calls, so the prosecution had 11,606 data points." But that is nothing, she says, compared to the warrantless data grabs that would be allowed by the court's "wooden application of the third-party doctrine":
Under a plain reading of the majority's rule, by allowing a third-party company access to our e-mail accounts, the websites we visit, and our search-engine history—all for legitimate business purposes—we give up any privacy interest in that information.
And why stop there? Nearly every website collects information about what we do when we visit. So now, under the majority's rule, the Fourth Amendment allows the government to know from YouTube.com what we watch, or Facebook.com what we post or whom we "friend," or Amazon.com what we buy, or Wikipedia.com what we research, or Match.com whom we date—all without a warrant. In fact, the government could ask "cloud"-based file-sharing services like Dropbox or Apple's iCloud for all the files we relinquish to their servers.
According to the third-party doctrine, such deeply personal and highly revealing information has only as much protection as legislators decide to give it. As Justice Sonia Sotomayor suggested in 2012, it is long past time for the Supreme Court to revisit this misbegotten principle, which was enunciated nearly four decades ago and becomes a bigger menace to our privacy every day.

