Instapundit: What If a Cyber-Pearl Harbor Happened and Nobody Noticed?
Writing in USA Today, Glenn Reynolds, the Interweb's Instapundit, makes the provocative case that the massive Chinese hacks of U.S. government personnel records and related material is akin to Pearl Harbor:
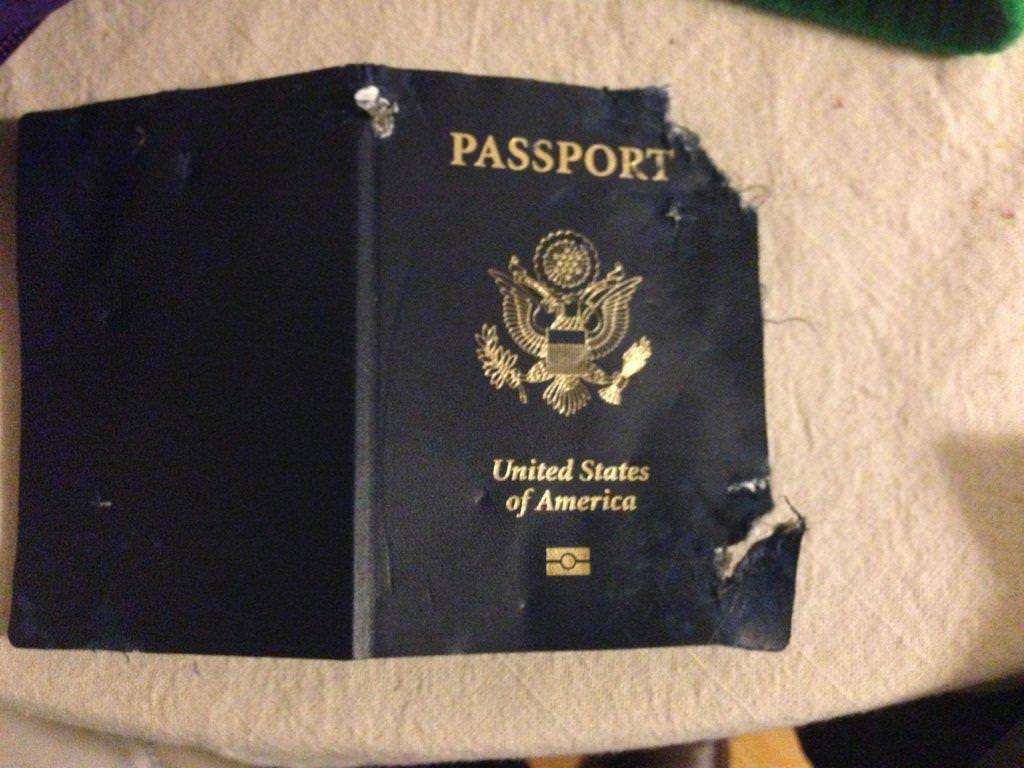
Aside from regular federal personnel records, which provide a royal route to blackmail, intimidation and identity theft for present and retired federal workers, the hackers also stole a trove of military and intelligence records that could be even more valuable. The forms stolen were Standard Form 86, in which employees in sensitive positions list their weaknesses: past arrests, bankruptcies, drug and alcohol problems, etc. The 120 plus pages of questions also include civil lawsuits, divorce information, Social Security numbers, and information on friends, roommates, spouses and relatives.
The result? About 14 million current and former federal employees are in a state of collective panic over the loss of their information. Former State Department employee Matthew Palmer was quoted as saying, "Who is in danger? I listed friends on those forms and my family members. … Are some hackers going to start going after them?"
And yet, Reynolds says, nobody seems to really give a hoot.
So far the federal government is offering free identity-theft protection to its employees, but that response is like putting a Band-Aid on a severed limb — so pathetic it's not even cosmetic. This isn't like a broken code, where we can just change things around and be almost as good as new. Once out, this information will remain current for years, and there's no easy or effective way of doing much about that.
Reynolds makes one odd (IMO) suggestion, which is that certain federal records should only be maintained in paper form (inefficient but incapable of being hacked as easily as digital copies, he claims), but this is certainly true:
The lesson is that we should probably think twice before entrusting the federal government with our own information. Because if the feds can't protect their own sensitive data, on behalf of people who work for the federal government, how good a job are they likely to do on behalf of the rest of us mere citizens?
LifeLock for the federal government? Sure, why not.
Oh, and there's this, via Investor's Business Daily:
Last July, the Department of Homeland Security discovered that hackers had breached OPM's [Office of Personnel Management] network and "appeared to be targeting the files on tens of thousands of employees who have applied for top-secret security clearances."
Less than a month later, USIS, a major federal contractor that does background checks for security clearances, reported that its network had been breached.
Then, in December, the OPM had to alert 48,000 federal employees about a cyberattack on KeyPoint Government Solutions, another private contractor that does background checks on federal employees.
Didn't it occur to anybody in this administration that maybe, just maybe, these attackers would keep trying?

