4 Reasons to Fear Encryption 'Back Doors,' Even Though You're Not a Terrorist
This seemingly simple demand opens a massive can of extremely dangerous worms.

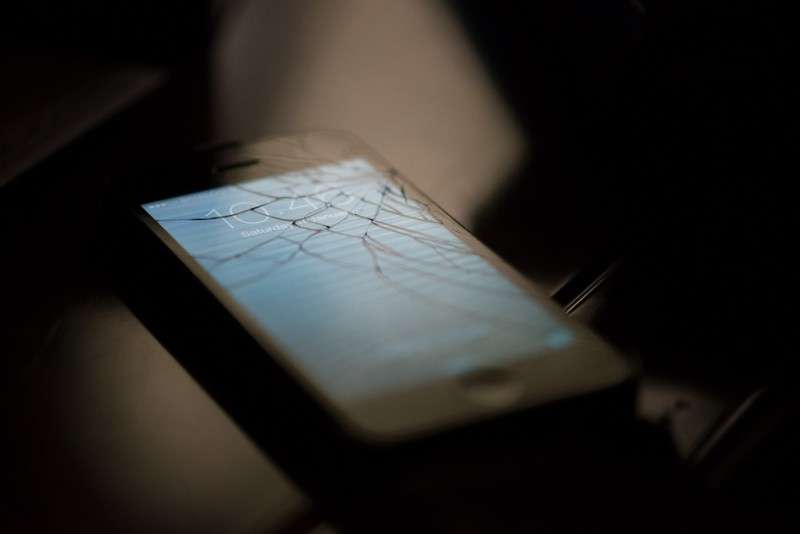
Apple's open resistance to a judge's orders to help the FBI crack the passcode for the iPhone owned by deceased San Bernardino terrorist Syed Farook has given some much wider attention to the debate over encryption.
On one side, we have law enforcement and some government officials saying they need to be able to get access to data that can help fight terrorism and serious crime. On the other side, we've got privacy advocates and tech experts worrying about how this power could potentially be abused and how it compromises the security of all our data and leaves us open to hackers, identity thieves, and other criminals.
Much in the vein of those who have decided not to worry about government surveillance of our online and phone communications because they have "nothing to hide," there are citizens who see only an effort to stop terrorism and not any of the other potential consequences. If you are one of those people (or you have people of that type in your life or Facebook feed), here are a sample of reasons why government "back door" access to encryption has the potential to cause harm to you, your family, and other people who are not terrorists trying to kill people.
1. This Is Much Bigger than Just Letting the Government Access a Single Phone
"Can't Apple just give them the information from this one phone?" That simple question is the basic frame for the debate. The judge's order demanding that Apple assist the FBI getting access to the contents of terrorist Syed Farook's phone attempts to set up a situation so that the feds would only be able to use this tool to access this one phone in Apple's presence.
Apple CEO Tim Cook's response to the public is that no, Apple cannot create a tool or program that can open just Farook's phone that cannot used again or—more importantly—cannot be replicated and abused by people with bad intentions: "Once the information is known, or a way to bypass the code is revealed, the encryption can be defeated by anyone with that knowledge."
And let's be very clear: The federal government's desire to get past encryption on smart phones is not limited to Farook. This is a test case. Federal law enforcement officials and intelligence agencies have been looking to find ways through encryption for decades now. As The Guardian noted in their reporting of the background of this fight, this case, if the FBI is successful, would create a precedent where the government would be able to conscript tech companies (even more than they already do) to help them investigate criminal suspects at the expense of the companies' own customers safety and security.
Therefore, even if Apple is actually able to create a program or tool that will open Farook's phone and only Farook's phone, there is absolutely no reason to believe that it will stop there. And ultimately, Cook's fears will eventually come true. The more the government turns to this method of trying to bypass encryption the more likely these tools will indeed end up getting out there in the world in the hands of hackers or crooks.
2. If the U.S. Can Demand IPhone Back Doors, Then So Can China, or Russia, or Iran, or Your Local Sheriff …
We can talk about the some of the ways America and other Western countries have less than stellar records respecting the civil liberties of their citizens, but they tend to pale in comparison to what goes on in other countries. People who speak out against their own government are jailed, or worse. The privacy of encrypted communications allows activism and defiance against oppressive regimes in a way that reduces potential risk. Officials demanding back doors on encryption propose that this effort fights only terrorism and crime and therefore saves lives. That's far from the whole picture. Encryption helps protect citizens from identity thieves and hackers, but also from snooping authoritarian regimes looking for dissidents to imprison. Encryption doesn't threaten lives—it can help protect lives.
Americans may see back doors solely as a tool to fight terrorism or other serious crimes. And that's exactly how supporters of encryption bypasses want Americans to see it. But these back doors are just a neutral tool that can be used for any number of purposes, many of them very, very bad. Congress, the president, and the FBI would not be the people having final say on what is and is not an acceptable use of an encryption back door.
3. Apple Made the Phone; It Doesn't Own It. What Does This Say About Control of Private Property?
Nobody in this dispute is arguing that the FBI lacks the authority to attempt to collect any property possessed by Farook as part of the investigation on the San Bernardino terrorist attack. Nobody is even arguing that the FBI or the federal government doesn't have the authority to attempt to crack Farook's phone security on its own.
There is, however, a mistaken comparison to the serving of a warrant to perform a search from those who would defend the FBI's order here. A search warrant is administered to the owner or resident of a property. Apple is not the owner of Farook's phone (technically, San Bernardino County is, which is perhaps causing some people to think about company or agency security guidelines). Cook pointed out that Apple does cooperate with authorities when given subpoenas for data that is under Apple's direct possession. And it has apparently done so for this very investigation.
But Farook's phone is not Apple's property. This is not data held by a third party. This is not the same as serving a search warrant to demand access to somebody's house. Rather, this is like serving an order to the company that manufactured the locks on the house's doors and telling them they have to come out and unlock them so that police can gain entrance. That's why the legal debate surrounding the judge's order is reliant on the All Writs Act, a law as old as the United States government that permits judges to demand citizens take defined actions to further its legal goals.
We do have some unusual circumstances here. Farook is dead, so the cooperation of the property's owner is out of the question. But, to reiterate a previous point, the federal government has made it very abundantly clear that they want to bypass encryption not just in this one case, but in others as well, including cases where the suspected criminal is alive but uncooperative or unavailable. The government is attempting to coerce citizens into assisting the government to gain access to somebody else's property. This sets a dangerous precedent that is easy to ignore because of the circumstances of this case.
Consider instead, though, this process being used against living people for cases that are going to get much less attention than a man responsible for the deaths of 14 people on American soil in a terrorist attack. Consider, oh, an IRS investigation instead. Cook warns that orders like this could be used to demand the building of "surveillance software to intercept your messages, access your health records or financial data, track your location, or even access your phone's microphone or camera without your knowledge."
Suddenly your property is not even your property. This isn't serving a warrant to search your home. This is sneaking into your home when you're not there and going through your drawers without you even noticing.
4. The Government Has a History of Abusing Surveillance Authorizations
We haven't forgotten about Edward Snowden, have we? His leaks revealed that the National Security Agency (NSA) was secretly abusing surveillance authorities provided by the PATRIOT Act in ways its author never intended (and a judge subsequently ruled never actually authorized): They were collecting telephone and Internet metadata from pretty much all Americans and storing it for use for allegedly track down terrorists. There was no evidence that this violation of our privacy ever actually helped prevent a terrorist attack. It certainly didn't help stop Farook.
Even right now we know that the American government continues to use surveillance to monitor activism by Americans just as his done in the days of the civil rights battles of decades ago. Groups critical of government behavior from the left, the right, and anywhere in between, discover that their participants and events, even when completely peaceful, are being monitored by federal officials worried about anti-government behavior.
And that's just on the federal level. On the local level, consider that the New York Police Department has engaged in inappropriately broad surveillance against Muslim people both in its city and in New Jersey and has possibly been using X-Ray devices to snoop. We have police departments secretly using Stingray devices to collect cellphone location data and trying to conceal their use from the courts and defendants. We have local government agencies reading and recording the license plate numbers of passing vehicles and then considering sending drivers threatening letters if they are seen areas frequented by prostitutes.
Even if the government itself doesn't implement policies to violate citizen privacy, there are frequently bad actors who work for the government who use access to information for sinister ends. We've seen everything from Miami police officers using the names of people in the state's driver's license database to file false tax returns to NSA employees using their surveillance authorities to snoop on the communications of potential romantic interests.
Ultimately, what the FBI is asking for leads to yet another potential surveillance tool with extremely high potential for abuse. And because Americans now use these phones for so much and they have so much information on them, arguably giving the government a back door into our phones is even more intrusive than having them inappropriately listening into our phone calls or reading our mail.

