Goofus and Gallant on Encryption and Government Intrusion
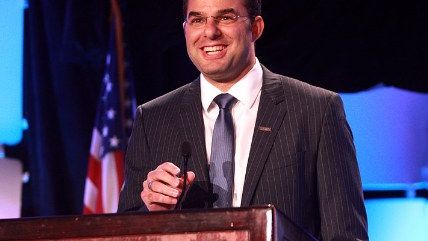
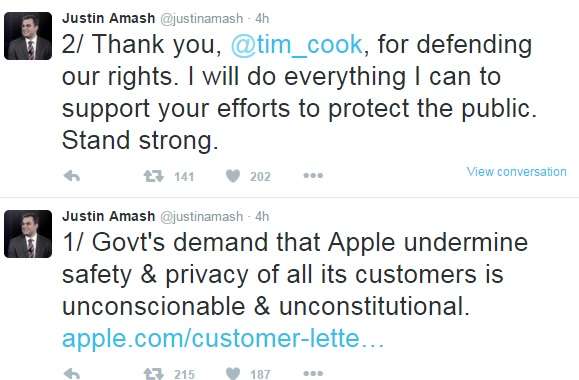
Consider Sen. Tom Cotton and Rep. Justin Amash and guess which is which.

Goofus, despite all historical warnings that this trade-off doesn't work out well for citizens, demands that we all choose security over privacy:
"Apple chose to protect a dead ISIS terrorist's p?rivacy over the security of the American people. The Executive and Legislative Branches have been working with the private sector with the hope of resolving the 'Going Dark' problem. Regrettably, the position Tim Cook and Apple have taken shows that they are unwilling to compromise and that legislation is likely the only way to resolve this issue. The problem of end-to-end encryption isn't just a terrorism issue. It is also a drug-trafficking, kidnapping, and child pornography issue that impacts every state of the Union. It's unfortunate that the great company Apple is becoming the company of choice for terrorists, drug dealers, and sexual predators of all sorts. "
Gallant pays attention and understands that encryption protects citizens from both private fraud and crime, as well as civil rights abuses from governments, both domestic and abroad:

Not up to speed on what's going on? Read here.

