Brickbat: Shall We Play a Game?
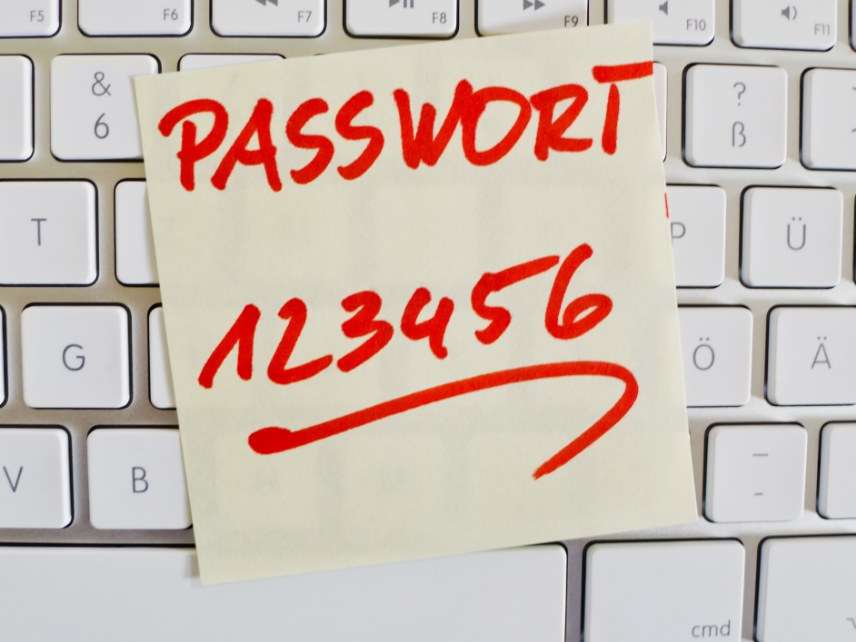
It started in seventh grade, when Jeremy Currier and Seth Stephens found a sticky note with log-in information on a computer in the school library. Using that information, they were able to access files created by staff. A couple of years later, in high school, they found another sticky note with log-in information on the laptop of a school security guard. They used that to take control of the school's security cameras. Eventually, they hacked all of their Michigan school district's computer systems. Even though, according to Education Week, there's no evidence they "cheated or changed grades, disrupted classes or sold answers to tests, zeroed out lunch balances or broke into anyone's locker, installed malware or deleted files, harassed people online or stole anyone's identity" the two were expelled when their exploits were finally discovered, and they are now the subjects of a criminal investigation.

