If You Bought Drugs on the Silk Road Using Bitcoin, the Feds Might Know Who You Are
If buying drugs online feels easy, you're probably doing it wrong.
If you've ever used bitcoin to buy drugs on the Silk Road, there's a nonzero chance that researchers in Qatar know your real name. In a paper published this month, Husam Al Jawaheri of Qatar University outlined the simple method that his team used to tie data from the open web—specifically, information shared on Twitter and in a popular bitcoin forum—to transactions that appeared on the bitcoin blockchain, the distributed and fully public database that lists transactions without connecting them to an identity or location.
By scraping sites on the dark web for bitcoin addresses and then cross-referencing them with those same addresses on the blockchain, Jawaheri's team was able to link 125 unique users to 20 Tor hidden services, "including sensitive ones, such as The Pirate Bay and Silk Road."
Moving bitcoin from one user to another requires posting to the blockchain "public keys," which are strings of letters and numbers in the possession of users. If you wanted to pay me in bitcoin, I would generate a receiving address (one of those strings) that you could use to send me currency. I wouldn't need to provide you with a username, email address, or anything tied to my identity. I could even post the receiving address online in the form of a QR code, so people can send me bitcoin without even knowing my real name.
If you are able to link my name to that address, however, the transaction is no longer anonymous; nor are any other transactions carried out with the same address.
The weakness that Jawaheri's team identified is that bitcoin enthusiasts over the years have given their public keys out to lots of people and posted them in lots of different places. Many of them did so using internet accounts on which they also posted bits and pieces of identifying information about themselves, even if they wrote under a pseudonym—things like where they live, what they do for work, where they went to school or grew up, how many kids they have, whether they're married. This thread on the forum Bitcoin Talk, which the Qatar University researchers scraped for public addresses, references a public spreadsheet full of public addresses.
Not everybody who used bitcoins to buy drugs on the Silk Road in the early 2010s is identifiable, but some appear to be very identifiable:
"There are 22 users that had a link to Silk Road through transactions with seized Bitcoin addresses. These users are located across the world in countries such as India, Canada, and the USA. They include 4 males and 6 females of different ages that range between 13 and 42 years. The 18 users from the forum dataset were active on BitcoinTalk between 2013 and 2015, while 3 of them are still active in 2017. As for the 4 users from the twitter dataset, they posted an average of 45 tweets in 2014. One particularly interesting user is a young teenager from the USA. This user has been a registered BitcoinTalk member since 2013, and had a transaction with Silk Road in 2013, the takedown year, during which he was even younger than what his current age shows on his profile. The associated profile also includes his personal website, which contains links to his Facebook, Twitter, and Youtube profiles."
It's a small group of people, so maybe it doesn't sound like a big deal. But Jawaheri's team was only, in its words, "a passive, limited adversary." They were just seeing what identifications they could make using data that were just lying around. Law enforcement, hackers, and other active investigators could surely dig up more.
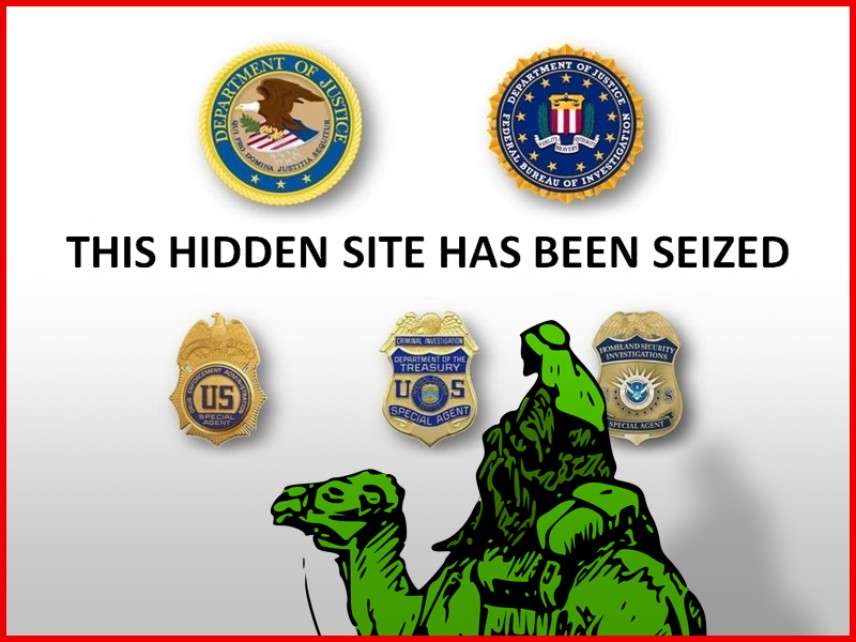
This isn't the first time researchers have found a way to identify bitcoin users. In 2014, computer scientists at Penn State proved it possible to associate bitcoin purchases on the open web with IP addresses, depending on traffic volume. But as far as I know, this is the soundest method anyone has devised for tying dark web activity to open web identities without actually commandeering a dark web server. The Justice Department now has servers from at least two sites—the Silk Road and AlphaBay—and it has already used years-old Silk Road data to build a very recent case against a group of marijuana vendors in California.
There are a number of things bitcoin users can do to keep their transactions not just private, but anonymous. "First, users should never expose their Bitcoin addresses along with their personally identifiable information," the researchers write. "Second, a new address should be generated for each transaction in order to reduce linkability of transactions, regardless of whether the user is the sender or the receiver of the payment. This is especially true for cases where users expose a donation address on different kinds of online social networks."
The researchers also mention the rise of monero, a cryptocurrency that many dark net customers claim is actually anonymous, if less commonly used and accepted. It's also worth looking into the process of "tumbling," which moves bitcoin purchased on a platform like Coinbase through a wallet that mixes users' bitcoin together, effectively obscuring who owns what.
Bitcoin Core, the community of cryptographers and engineers developing the open-source software that runs the network, are also working on a variety of privacy-enhancing technologies, including a new system for aggregating public keys, and a technique that would make it harder to link a transaction to an IP address.
Many people have bought personal quantities of drugs online over the years, and law enforcement has neither the time nor the interest in harassing and surveilling every single one of them. But this study should serve as a wakeup call to anyone who sees the dark web as a convenient place to buy illegal substances. If buying drugs online feels easy, you're probably doing it wrong.

