80 Percent of Americans Want to Label Food That Contains DNA
Sigh.
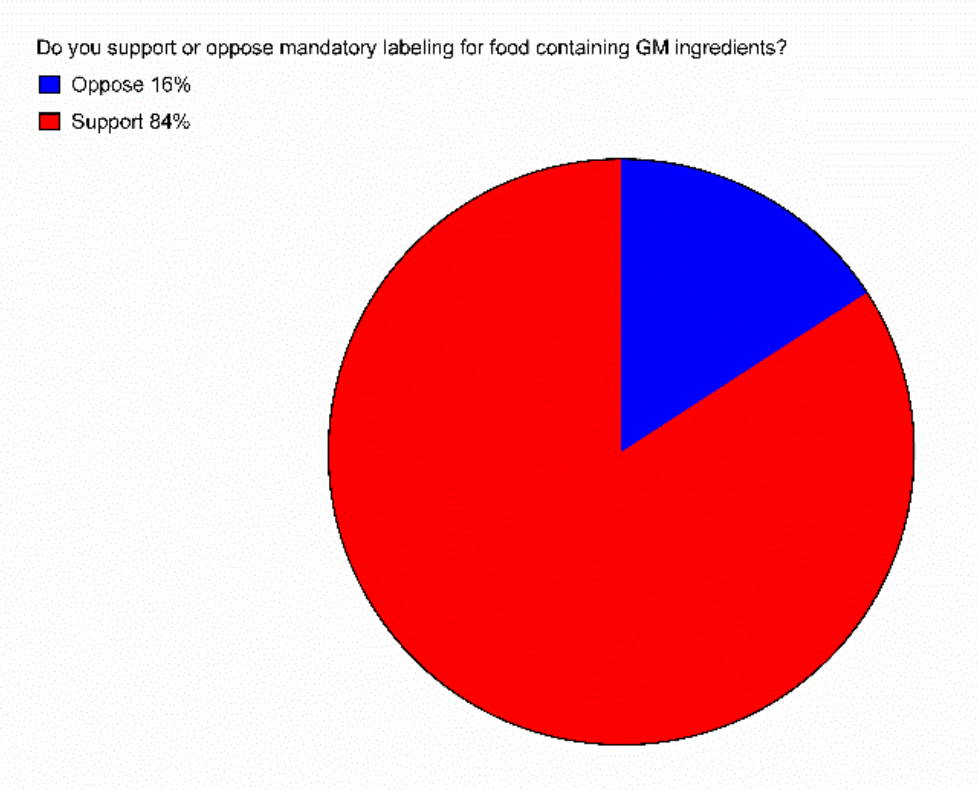
You might have heard that Americans overwhelmingly favor mandatory labeling for foods containing genetically modified ingredients. That's true, according to a new study: 84 percent of respondents said they support the labels.
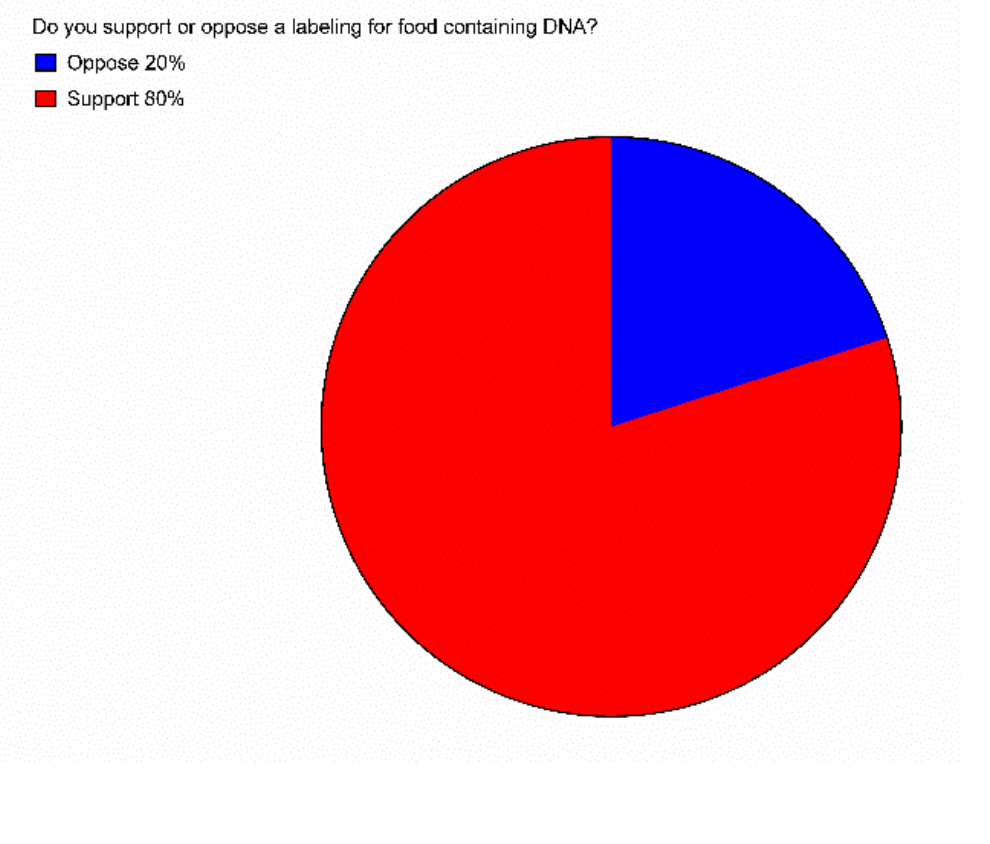
But a nearly identical percentage—80 percent—in the same survey said they'd also like to see labels on food containing DNA.
DNA.
The study, published in the Federation of American Societies for Experimental Biology Journal last week, also found that 33 percent of respondents thought that non-GM tomatoes "did not contain genes" and 32 percent thought that "vegetables did not have DNA." So there's that.
University of Florida food economist Brandon R. McFadden and his co-author Jayson L. Lusk surveyed 1,000 American consumers and discovered that "consumers think they know more than they actually do about GM food." In fact, the authors say, "the findings question the usefulness of results from opinion polls as motivation for public policy surrounding GM food."
My summary for laymen: When it comes to genetically modified food, people don't know much, they don't know what they don't know, and they sure as heck aren't letting that stop them from having strong opinions.
However, the authors do offer another, more charitable way to read their findings, suggesting that rather than simply throw up our hands and say that Americans are the Jon Snows of GM food, we should consider the possibility that the results "indicate how consumers psychological[ly] handle difficult questions."
Perhaps "individuals attempt to economize on scarce cognitive resources by unconsciously substituting an easier question for a hard one. Rather than seriously weighing the pros and cons of a mandatory labeling, the similarity in responses to the DNA labeling question suggests people may instead be substituting these questions with a simper question like, 'do you want free information about a topic for which you know very little?' This psychological process would lead to similar levels of support to two very different policy questions." Leaving aside the sick burn implied by the phrase "scarce cognitive resources" for a minute, this is a good point.
What's more, the researcher found that even posing basic questions about GM food caused people to re-evaluate how much they knew, downgrading their own perceptions of their knowledge levels, while simultaneously becoming more confident about the safety of GM foods.
UPDATE with fun fact: High fructose corn syrup and other highly refined foods made with GM crops actually don't contain DNA, apparently.


