Federal Agency Wastes $2.7 Million Fighting Practically Nonexistent Cyber Attack
Here's what happened when a tech-inept federal agency panicked over a potential cyber threat: The Economic Development Administration last year blew half its information technology budget fighting phantom attacks, cutting off staff from basic communications systems like email, and unnecessarily destroyed hundreds of thousands of dollars worth of computer equipment that not only wasn't infected but almost certainly couldn't have been infected — stopping only when the agency ran out of funding to destroy equipment.
Federal News Radio has the whole sad, sorry story, based on a new report from the Department of Commerce's Office of Inspector General:
The Commerce Department's Economic Development Administration spent almost half of its IT budget last year to remediate a cyber attack that barely happened.
Commerce's inspector general found in a report released last week a string of errors and miscommunications led to EDA's overreaction of removing employee email and website access from the main agency network.
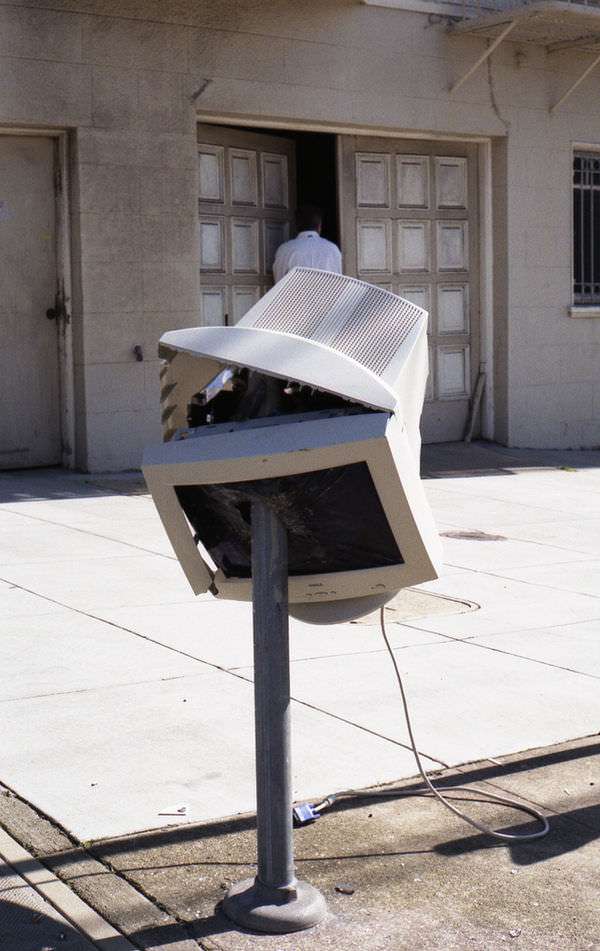
EDA's drastic steps to limit the damage by shutting down much of the access to the main Herbert Hoover Building network ended up costing the agency more than $2.7 million to clean up and reconfigure its network and computers. The IG said the bureau destroyed more than $170,000 in IT equipment, including desktop computers, printers, keyboards and mice.
But the IG found no evidence of a large scale malware attack, and in fact, a series of blunders between EDA and the Commerce Department's incident response team led to what turned out to be poor decisions by senior leaders, a waste of money and resources and potentially a disruption to EDA's mission.
You can see a number of problems here: One is just the general technological incompetence of the EDA. Based on an initial report from the incident response team, the agency's IT administrators apparently thought that 146 components were infected throughout their network. But when the incident response team corrected their report to say that in fact only two components appeared to be infected, the EDA IT team did not understand the update, according to the FNR report. Indeed, it appears as if the EDA IT team didn't understand basic details about their own network setup. Basically, the whole thing was one giant, cascading ID-10-T error.
According to Ars Technica, malware was eventually found on about half a dozen EDA computer systems, but they could have been cleaned up simply by doing a clean system wipe and starting over.
Another is that fear of massive cyber attacks led to a huge overreaction. FNR notes that the agency's chief tech official thought a serious, sophisticated cyber-attack was "highly probable and possible." But the malware they found wasn't part of some big international attack. It was common Internet garbage, the sort of crapware that barely counts as a cyber threat at all, much less an actual "attack."
The ensuing panic didn't just end up wasting money. It ended up wasting time and effort that might have gone to actually securing the agency's systems, which were completely open to exploits. As Ars explains, the IG report indicates that "the EDA's IT infrastructure was so badly managed and insecure that no attacker would need sophisticated attacks to compromise the agency's systems."
Read Jerry Brito and Tate Watkins on the great cyber security panic, and the dubious but incredibly expensive cybersecurity-industrial complex that has grown up around it, in Reason's August 2011 issue.

