New Snowden Profile in Wired Reveals New NSA Secrets Like 'MonsterMind'
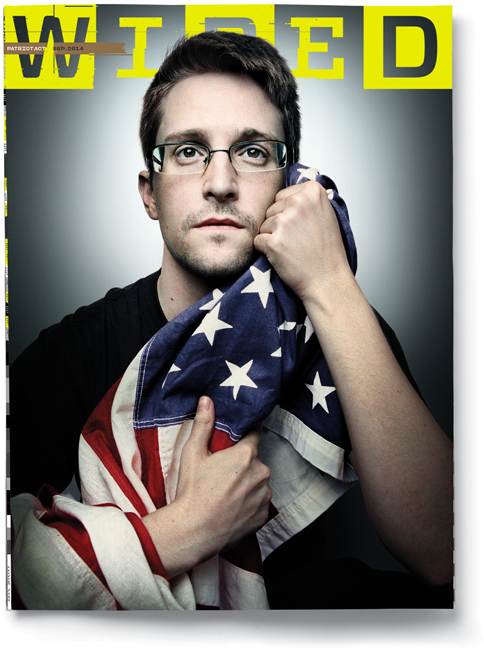
James Bamford, the national security journalist and author who himself had once been threatened with prosecution over his writings about the National Security Agency's (NSA) activities decades ago, has gone to Russia to sit down with Edward Snowden. From the meeting, he put together a profile of the NSA whistleblower for a massive piece in Wired magazine.
In addition to the typical biographical background and the description of how Snowden's life is playing out in Russia (pretty tame—Snowden doesn't appear to get around much), Bamford came back with two new scoops.
First, back in 2012 Syria had a major Internet outage amidst its civil war. Naturally, people assumed this was done somehow by President Bashar al-Assad or loyalists in order to censor opposition. It was not. It was caused by the United States, and it was an accident:
One day an intelligence officer told [Snowden] that TAO—a division of NSA hackers—had attempted in 2012 to remotely install an exploit in one of the core routers at a major Internet service provider in Syria, which was in the midst of a prolonged civil war. This would have given the NSA access to email and other Internet traffic from much of the country. But something went wrong, and the router was bricked instead—rendered totally inoperable. The failure of this router caused Syria to suddenly lose all connection to the Internet—although the public didn't know that the US government was responsible. (This is the first time the claim has been revealed.)
Inside the TAO operations center, the panicked government hackers had what Snowden calls an "oh shit" moment. They raced to remotely repair the router, desperate to cover their tracks and prevent the Syrians from discovering the sophisticated infiltration software used to access the network. But because the router was bricked, they were powerless to fix the problem.
Fortunately for the NSA, the Syrians were apparently more focused on restoring the nation's Internet than on tracking down the cause of the outage. Back at TAO's operations center, the tension was broken with a joke that contained more than a little truth: "If we get caught, we can always point the finger at Israel."
So if the outage did actually hamper efforts to dislodge Assad—and remember U.S. leaders were publicly calling for him to step down at this time—they have us to thank.
The bigger revelation is the existence of MonsterMind, which is not the name of Lady Gaga's next album. It is the reason why the NSA really, really needs to be connected to everybody online, all the time:
The massive surveillance effort was bad enough, but Snowden was even more disturbed to discover a new, Strangelovian cyberwarfare program in the works, codenamed MonsterMind. The program, disclosed here for the first time, would automate the process of hunting for the beginnings of a foreign cyberattack. Software would constantly be on the lookout for traffic patterns indicating known or suspected attacks. When it detected an attack, MonsterMind would automatically block it from entering the country—a "kill" in cyber terminology.
Programs like this had existed for decades, but MonsterMind software would add a unique new capability: Instead of simply detecting and killing the malware at the point of entry, MonsterMind would automatically fire back, with no human involvement. That's a problem, Snowden says, because the initial attacks are often routed through computers in innocent third countries. "These attacks can be spoofed," he says. "You could have someone sitting in China, for example, making it appear that one of these attacks is originating in Russia. And then we end up shooting back at a Russian hospital. What happens next?"
In addition to the possibility of accidentally starting a war, Snowden views MonsterMind as the ultimate threat to privacy because, in order for the system to work, the NSA first would have to secretly get access to virtually all private communications coming in from overseas to people in the US. "The argument is that the only way we can identify these malicious traffic flows and respond to them is if we're analyzing all traffic flows," he says. "And if we're analyzing all traffic flows, that means we have to be intercepting all traffic flows. That means violating the Fourth Amendment, seizing private communications without a warrant, without probable cause or even a suspicion of wrongdoing. For everyone, all the time."
Read the whole story here, including explanations why Snowden ended up dropping out of high school as a teen and what happened next (if you're thinking detractors have left out important details, you're right), Snowden's explanation that he left clues so NSA could determine how many documents he actually took with him (they still don't know), and more potential confirmation that there is at least one other NSA leaker out there.
